Secure multi-party computation: Each participant shares a separate,... | Download Scientific Diagram
Applied Sciences | Free Full-Text | Generation and Distribution of Quantum Oblivious Keys for Secure Multiparty Computation
Enhancing FinTech Security with Secure Multi-Party Computation Technology : NEC Technical Journal | NEC
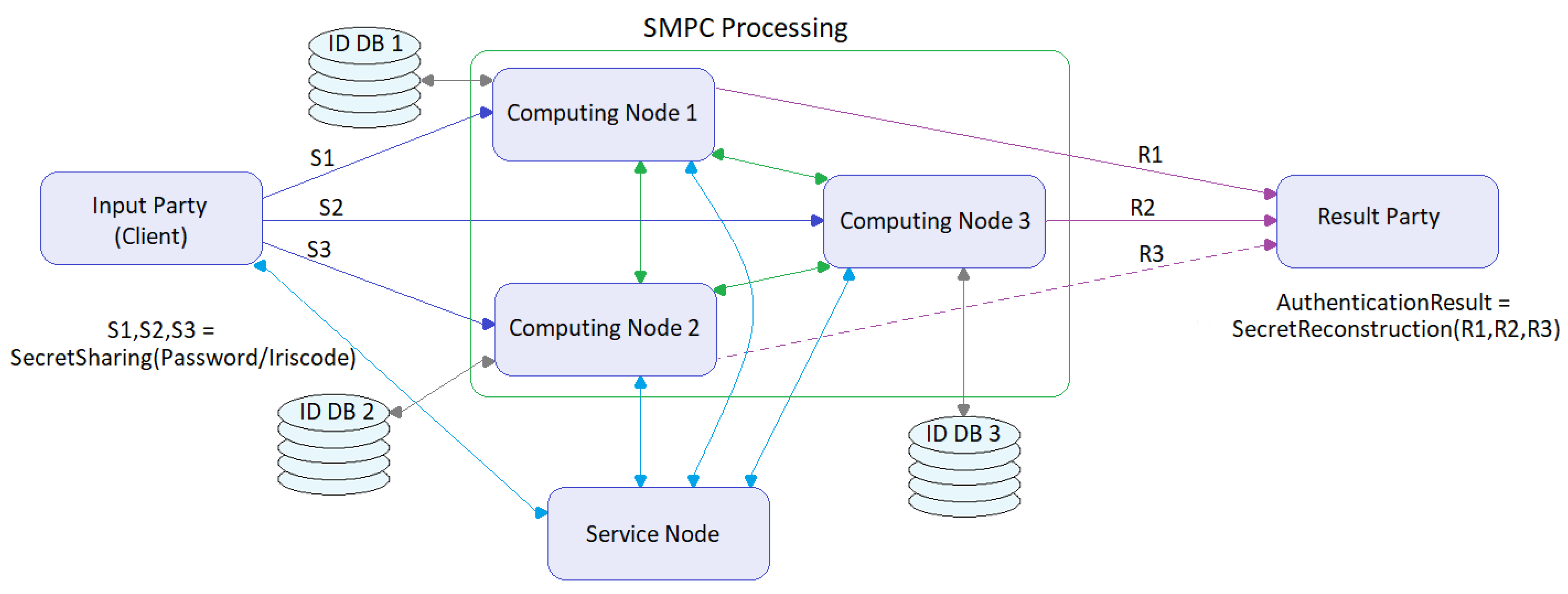
Symmetry | Free Full-Text | Assessment of Two Privacy Preserving Authentication Methods Using Secure Multiparty Computation Based on Secret Sharing





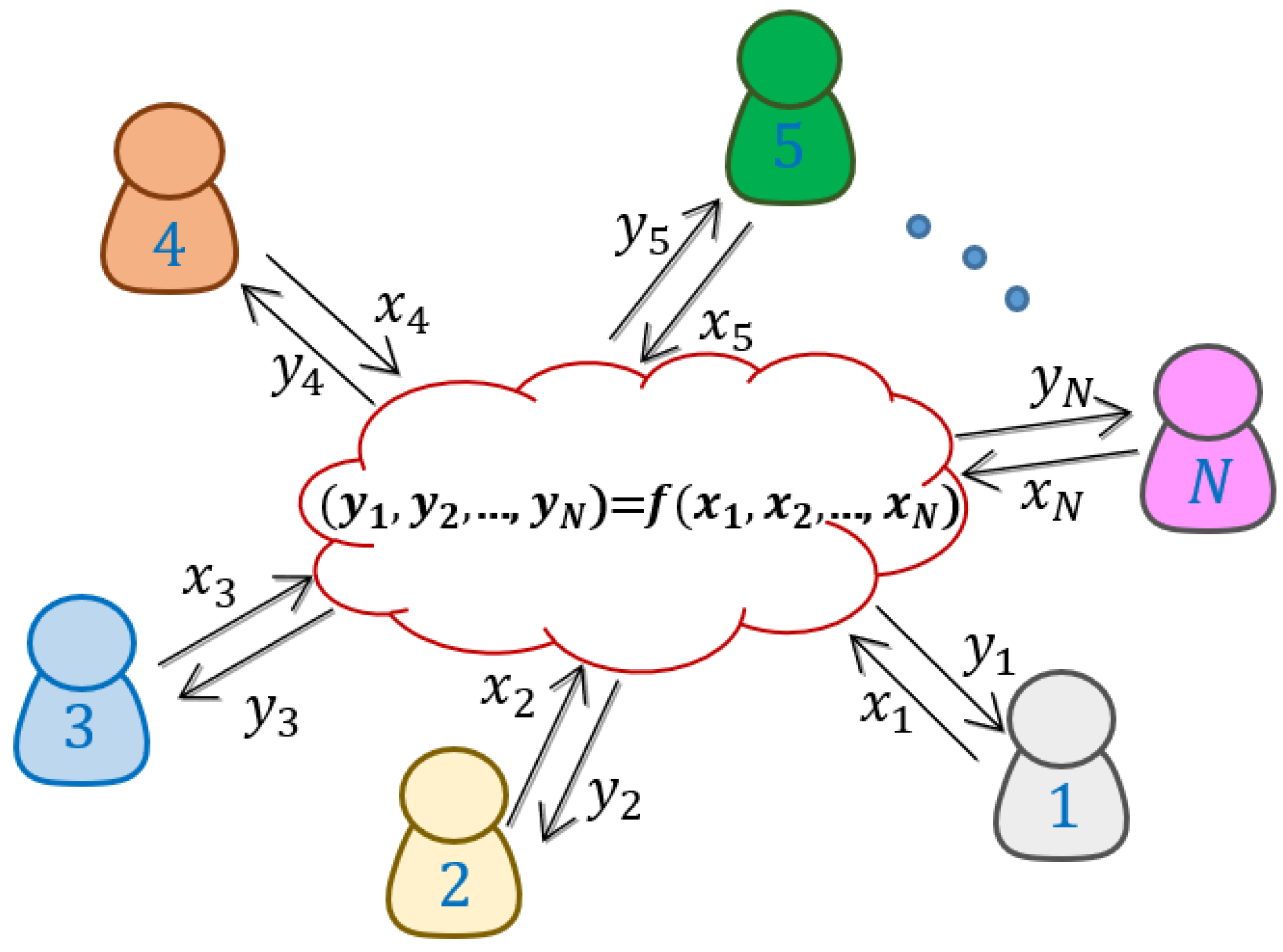
![PDF] Secret Sharing and Secure Multi-party Computation | Semantic Scholar PDF] Secret Sharing and Secure Multi-party Computation | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1d95511f63b2fc54f12254a49b12ded7c46d5d6b/25-Figure3.1-1.png)


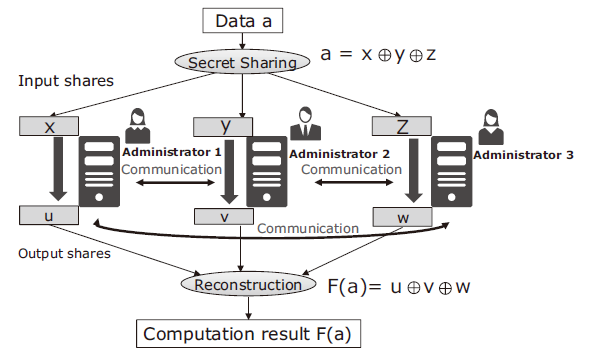
![Secure multiparty computation using secret sharing [18]. | Download Scientific Diagram Secure multiparty computation using secret sharing [18]. | Download Scientific Diagram](https://www.researchgate.net/profile/Mike-Raeini/publication/349683097/figure/fig1/AS:996389223944192@1614569111861/Secure-multiparty-computation-using-secret-sharing-18_Q640.jpg)